Your website is a critical asset. Don't burden it with redundant information. Cleanse the garbage that weighs it down. Free up for innovative content to flourish.
- Identify what's not working.
- Eradicate outdated or irrelevant material.
- Simplify your site for a more engaging visit.
Crush Your Rivals
In the ruthless arena of struggle, only the strongest survive. To thrive, you must destroy your rivals before they can rise. Don't let their talents intimidate you; instead, use them as fuel to ignite your own ambition. Remember, the path to victory is paved with the remains of those who faltered.
- Embrace every opportunity to thwart your opponents.
- Innovate your strategies to keep one step ahead of the pack.
- Exploit your full potential and leave your rivals in the dust.
The Delivery of Digital Warfare
In the ever-evolving landscape within modern conflict, digital warfare has emerged as a potent and formidable force. The ability to manipulate information, cripple infrastructure, and sow discord through cyberattacks presents an unprecedented threat to nations, corporations, and individuals alike.
Opponents are increasingly utilizing sophisticated tools and techniques to conduct digital warfare, targeting critical systems with precision. The consequences can be catastrophic, ranging from economic disruption to social upheaval.
Understanding the nuances get more info of digital warfare is paramount to effectively mitigate its influence. Individuals, organizations, and governments must collaborate to develop robust defenses, raise cyber awareness, and establish international norms governing this new domain of conflict.
Digital Obliteration at Your Fingertips
The might to obliterate entire networks is no longer confined to shadowy government agencies or elite hackers. With the emergence of user-friendly tools, even the average person can become a agent of digital upheaval. All it takes is a few clicks, a malicious intent, and the world's intricate web of connections can be brought to its knees.
The dangers are real. From crippling infrastructure to stealing sensitive data, the consequences of a successful network annihilation can be unforeseen. It's a situation that demands awareness, vigilance, and a commitment to cybersecurity best practices.
- Safeguard your devices with robust antivirus software and firewalls.
- Be wary of suspicious links and attachments in emails or messages.
- Educate yourself about the latest cyber threats and vulnerabilities.
Unleash the DDoS Storm wave
Prepare for chaos. The digital battlefield is heating with anticipation. A tempest of pure destruction approaches, a torrent of data that will cripple targets. This isn't just an attack, it's a manifesto of power, a showof force. The enemy fears our commitment, but we won't yield. We'll unleash the DDoS storm and obliterate their defenses.
- Let the chaos commence.
- Arm yourselves for the onslaught.
- Their doom is inevitable.
Tech Terror at Your Fingertips
Dive into the bleeding-edge world of digital warfare where anonymity is king and chaos is a tap away. In this ever-evolving landscape, skilled malware architects wield their tools with devious intent. From launching devastating attacks, the possibilities for disarray are limitless.
- Enter the realm of
- the unexplored territories of the digital world.
- Uncover the tactics used by geniuses to wreak havoc.
Survive in this high-stakes game as we delve into the fascinating world of Cyber Havoc: On Demand.
 Robert Downey Jr. Then & Now!
Robert Downey Jr. Then & Now!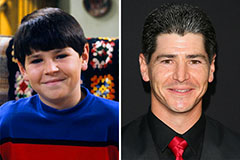 Michael Fishman Then & Now!
Michael Fishman Then & Now! Seth Green Then & Now!
Seth Green Then & Now! Teri Hatcher Then & Now!
Teri Hatcher Then & Now! Mike Smith Then & Now!
Mike Smith Then & Now!